Automatic Security Auditing for Your Private Packages
Pricore v0.50.0 introduces Security Auditing. Pricore now automatically checks your hosted packages for known security vulnerabilities by syncing advisories from the Packagist Security Advisories database. When a vulnerability is found, your team gets notified.
The problem
Public packages on Packagist benefit from a well-established vulnerability disclosure ecosystem. Private packages don’t get the same treatment. If one of your internal packages depends on a library with a known CVE, there’s no built-in way to find out. You’d have to run composer audit manually across every project and hope nothing slips through the cracks.
For most teams, that means vulnerabilities in private packages go unnoticed until something breaks.
How it works
Pricore syncs security advisories from Packagist every 4 hours alongside your mirror syncs. Each advisory includes affected package names, version constraints, CVE identifiers, and severity ratings.
When advisories sync or new package versions are added, Pricore matches them against your packages using Composer’s semver constraint checking. Two types of matches are detected:
- Direct: The package itself appears in an advisory
- Dependency: A package listed in
requireorrequire-devappears in an advisory
Organization owners and administrators receive email notifications when new vulnerabilities are detected. Emails include severity breakdowns, affected advisory titles, and a direct link to your security overview.
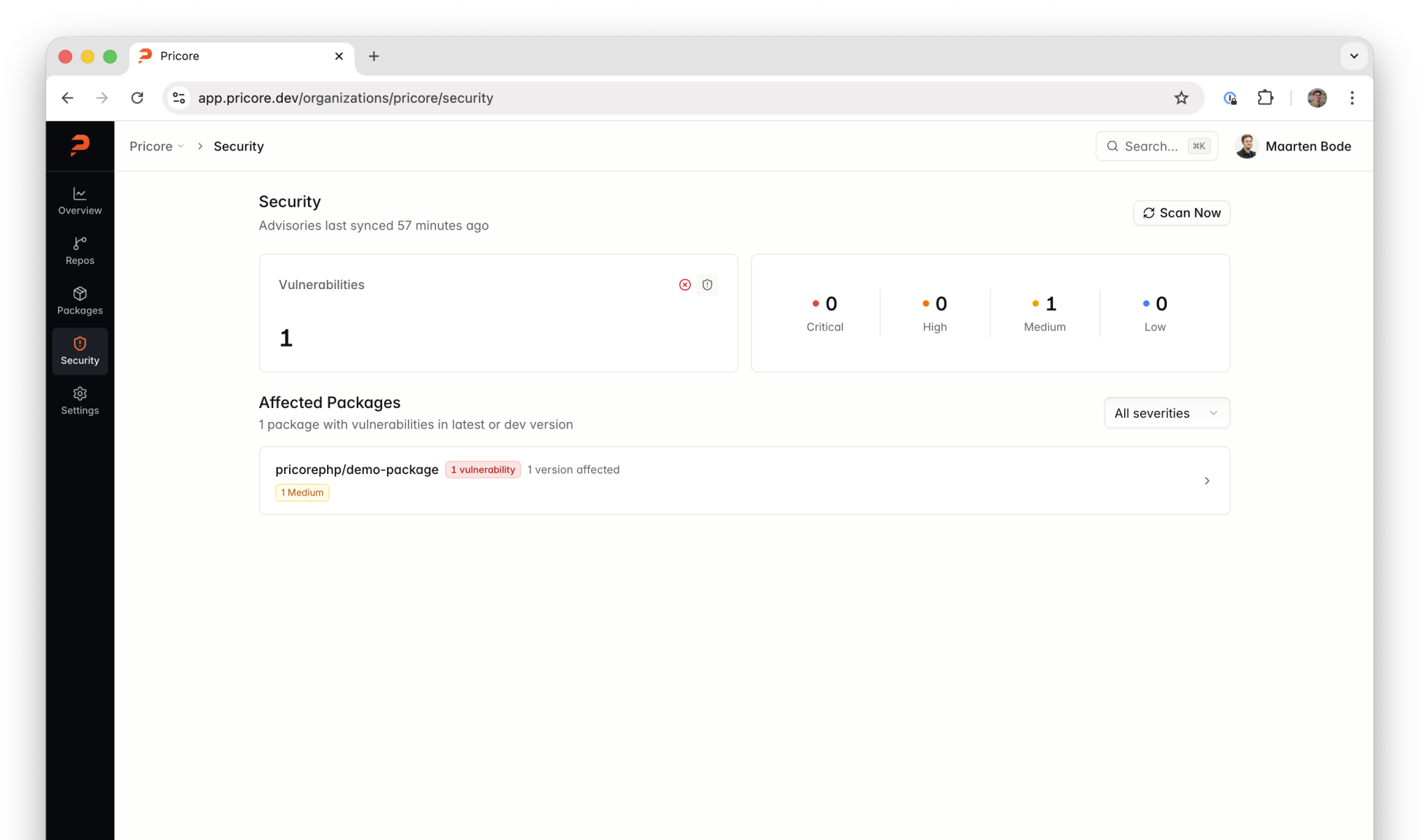
Security overview
Each organization gets a dedicated Security page accessible from the sidebar. It shows vulnerability counts organized by severity (critical, high, medium, low), a list of affected packages, and the latest stable and dev versions checked. You can filter by severity level to focus on what matters most.
On individual package pages, vulnerability badges appear next to affected versions. Red for critical or high severity, amber for medium, blue for low. Click a version to see the full list of matched advisories with CVEs, severity, and disclosure links.
Works with composer audit
Pricore implements the Packagist-compatible security-advisories endpoint, so composer audit works natively against your private registry. No extra configuration needed beyond your existing repository setup:
composer auditGet started
- Documentation: Security Auditing guide
- Cloud: Start your 14-day free trial
- Self-hosted: View on GitHub
